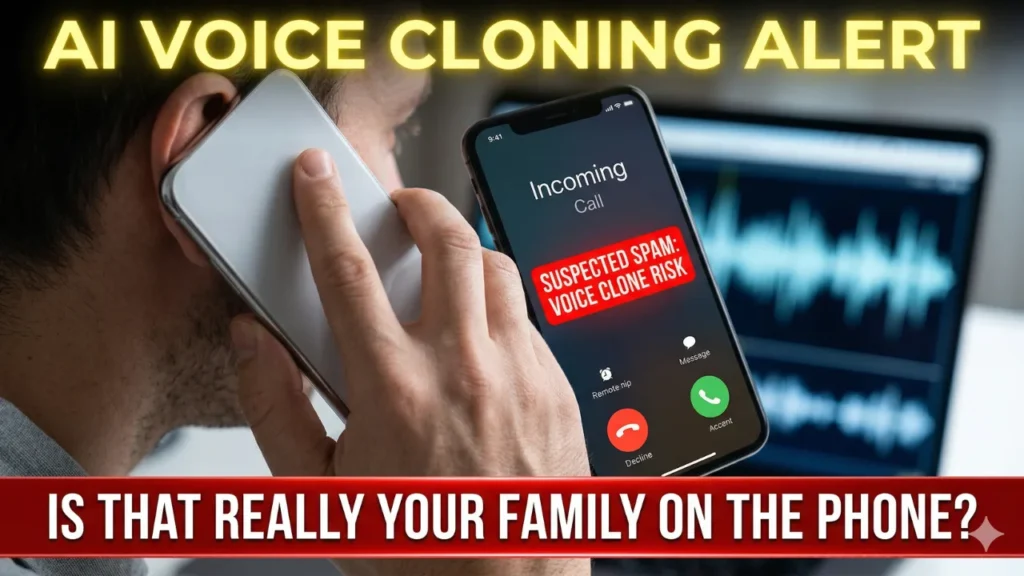
Stop AI voice scams before they quietly drain your hard-earned savings. In 2026, cybercriminals are heavily targeting families especially those with relatives working far away or Overseas Filipino Workers (OFWs) using terrifyingly accurate artificial intelligence. By simply extracting a brief, three-second audio clip from a public Facebook or TikTok video, hackers can perfectly clone your loved one’s exact voice. They will then call you, sounding incredibly panicked, claiming they are in a sudden emergency and urgently need funds transferred via e-wallets or bank deposits.
Negotiate Your Rent 2026: Stop Paying the Increase
Because our platform provides information only and is not an official site for financial deals or property sales, our primary goal today is purely educational. We want to equip you with the exact knowledge needed to identify these digital illusions and protect your personal wealth.
Key Takeaways for Digital Safety
- The Threat: Scammers use easily accessible AI software to flawlessly mimic the voices of your friends and family members.
- The Trap: They create a false sense of extreme urgency to force you to send money immediately without thinking.
- The Solution: You must verify every single emergency call independently before opening your banking applications or sharing personal details.
Grocery Saving Hacks 2026: Beat Supermarket Traps
How to Stop AI Voice Scams
The technology behind these modern attacks is highly sophisticated, but the ultimate defense against them relies on basic human communication. To effectively stop AI voice scams, you must implement a strict verification protocol within your household. Here is your step-by-step guide to securing your family’s daily communications:
- Establish a Family Safe Word: Sit down with your relatives today and agree on a unique, random safe word (like “Blueberry” or “Mango”). If a loved one calls claiming to be in an emergency, ask them for the safe word. An AI clone generated by a hacker will not know it.
- Disconnect and Verify: If the caller sounds exactly like your sibling but is demanding urgent money, immediately hang up the phone. Do not engage in conversation. Dial their exact phone number directly from your own saved contact list to verify their actual safety.
- Lock Down Social Media: Criminals desperately need source audio to clone a voice. Go into your social media settings right now and change your profile visibility from “Public” to “Friends Only.” Restricting access to your personal videos makes it incredibly difficult for hackers to gather your voice data.
- Question the Payment Method: Scammers will almost always demand fast, untraceable payment methods, such as anonymous e-wallet transfers or digital gift cards. Legitimate medical authorities will never demand instant digital transfers over the phone.
Work From Home Jobs 2026: Find Legitimate Remote Work
Frequently Asked Questions (FAQs)
How realistic do these cloned voices actually sound?
The technology in 2026 is nearly flawless. The artificial intelligence can replicate specific accents, breathing patterns, and even the emotional distress in a person’s voice, making it almost impossible to detect the fraud by sound alone.
Can local authorities easily stop AI voice scams?
Unfortunately, it is very difficult. Because these modern cybercriminals often operate internationally and use spoofed phone numbers to mask their location, tracking the origin of the call and recovering stolen funds is extremely challenging for law enforcement.
What should I do if I receive a suspicious emergency call?
Stay entirely calm. The scammers rely entirely on your panic. Ask the caller a highly specific personal question that only the real person would know—such as the exact name of their first childhood pet—before you take any financial action.
Are these attacks only targeting wealthy individuals?
No. Anyone with publicly accessible videos on the internet is a potential target. Hackers use automated software to scan social media platforms and execute these attacks on a massive scale against everyday citizens.
Prevent Car Theft 2026: Stop Keyless Entry Hacks

Diana Luci is a Senior Financial Analyst and Policy Researcher based in the US. She specializes in breaking down complex government updates, IRS changes, and economic trends into clear, actionable insights for everyday Americans.